On June 1st, Time announced that its MySpace social network had been compromised, and that account information for hundreds of millions of MySpace users with accounts created prior to June 2013 had been leaked. With the rise of networks like Facebook in recent years, MySpace has experienced decreasing relevance as time has gone by. This has resulted in this news being viewed as a point of amusement more than significant issue. However, there is a more significant issue created by this breach, and is one of the more fundamental and common security problems users of Internet services face. Luckily, it is one that is easy to remedy at the sacrifice of a little convenience. To explain this, I will begin with a cautionary tale. One that begins on Super Bowl Sunday, February 6th, 2011.
It was an ordinary Sunday for most of America. While many were preparing snacks and arranging to watch Pittsburgh and Green Bay face each other in Cowboys Stadium, a small group that would eventually call themselves Lulzsec, an offshoot of Anonymous were preparing to unveil to the world the results of a successful operation they had been executing. Their target was Aaron Barr. Aaron was the CEO of HBGary Federal, a cyber-security firm serving the federal government who was preparing to publish research he was performing to identify key Anonymous members.
This team managed to compromise the HBGary Federal website, and  decrypt the passwords used to manage the website. With this information, the hackers had his email address and his decrypted password. Under normal circumstances, this should have limited the damage to the hackers simply defacing the website, as they had done in many previous incidents. However, this time, Aaron used the same password on the website as he had for his email: “kibafo33.†Soon, the hackers had access to his email account and thousands of confidential correspondences. Unfortunately, it didn’t stop there either.
decrypt the passwords used to manage the website. With this information, the hackers had his email address and his decrypted password. Under normal circumstances, this should have limited the damage to the hackers simply defacing the website, as they had done in many previous incidents. However, this time, Aaron used the same password on the website as he had for his email: “kibafo33.†Soon, the hackers had access to his email account and thousands of confidential correspondences. Unfortunately, it didn’t stop there either.
Aaron had recycled this password in nearly every online service for which he signed up. Before long, the hackers had access to his Twitter account, Facebook, Flickr, Yahoo and even his World of Warcraft accounts. In truth, having access to his email account would probably have provided access to these anyway, but his habit of password recycling simplified things considerably.
As the opening kickoff proceeded, all of Aaron Barr’s accounts came to life, posting offensive taunts. HBGary Federal’s homepage was replaced with a notice by Anonymous. His emails were posted publicly for anybody to download and review. As a security research firm, this was not just and embarrassment, it was devastating to their reputation. Aaron would resign his position twenty days later.
What makes this noteworthy is that this was a security professional, which highlights the fact that password recycling is a common and pervasive problem. A problem of which most internet users are still unaware, six years later. This practice derailed a career and discredited a company, but this is not a problem that is limited to someone that pokes the hornet’s nest and is singled out by a hacking collective. Attacks today may have a far more lucrative motivation today than they have had in the past.
When MySpace was compromised, it was announced that account information for users with accounts older than June 2013 were taken. While details are still being revealed, there are two items that you can assume were part of this data theft: Email addresses and passwords. These two data points were the same data points used to devastating effect on Aaron Barr.
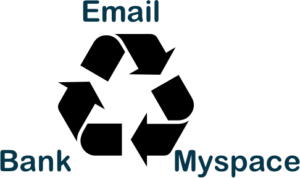
A number of people may have read this news and dismissed it. “So what if they access my Myspace account. I haven’t used it in years and don’t think anybody looks at it anywayâ€. “Ok, I guess I have to login and change my MySpace password now.â€Â These comments reflect a superficial view of the possible impact of this breach. For many users, the email address and password pair has not changed since 2013, and is probably the password to their email account, as well as access to other social media accounts. Unfortunately, it doesn’t stop there.
Once an intruder has gained access to your primary email account, he has the ability to act on your behalf and assume your identity with a number of other sites. Many now link their online banking with their email address. Once an intruder has access to your email, he often has access to your bank account and banking records. And online storefronts. Amazon, eBay, PayPal and more all rely on the inherent trust of the person in control of the linked email address. Access to your email often give the user the power to change passwords and access nearly any other service the user uses.
When a breach occurs on a site like MySpace, the recommendation should not just be to change the password on the compromised website, but also to change any other service where that same password was used. Most importantly, it is vital to keep your email password safe, as this is often the fulcrum of many other attacks.
Reactive measures aside, the better practice is to avoid reusing passwords all together. Each site or service you use should have a unique and complicated password. In this way, if one password becomes compromised, it will only provide access to the compromised service and provide no access beyond that service, effectively isolating any effect of a breach.
To understand the problem, though, you need to understand the cause. Good passwords are inconvenient. It is hard enough remembering one password that abides by all the rules that sites are starting to use now. Passwords are required to include numbers, special characters, lower and capital letters.
 To create a new and password that meets all of these criteria for every website is difficult, and remembering them is impossible. The temptation will be to use slight changes to one password that will be easy to remember. For example, if you use “PasswOrd†as your main password, you may use “PasswOrdF†for Facebook and “PasswOrdT†for Twitter. While this sounds like a good solution, if it is easy for you to figure out, it is just as easy for a hacker to derive as well. This is the cause of the fundamental problem. Security is frequently balanced against convenience, and convenience frequently wins the battle if the risk is not well understood.
To create a new and password that meets all of these criteria for every website is difficult, and remembering them is impossible. The temptation will be to use slight changes to one password that will be easy to remember. For example, if you use “PasswOrd†as your main password, you may use “PasswOrdF†for Facebook and “PasswOrdT†for Twitter. While this sounds like a good solution, if it is easy for you to figure out, it is just as easy for a hacker to derive as well. This is the cause of the fundamental problem. Security is frequently balanced against convenience, and convenience frequently wins the battle if the risk is not well understood.
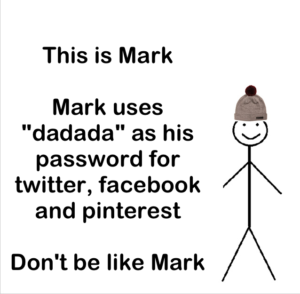 If you are not using strong passwords, or if you are using the same password for multiple or all of your accounts, you are in good company. Mark Zuckerberg, the CEO of Facebook was also hacked this week when his Twitter and Pinterest accounts were compromised. This occurred when the passwords stolen from a breach at LinkedIn during a 2012 event were published, and his password was revealed to be “dadada.” Even when you are the head of a company that handles some of the most private and intimate details of peoples lives, the temptation to chose something easy and memorable wins out over safety.
If you are not using strong passwords, or if you are using the same password for multiple or all of your accounts, you are in good company. Mark Zuckerberg, the CEO of Facebook was also hacked this week when his Twitter and Pinterest accounts were compromised. This occurred when the passwords stolen from a breach at LinkedIn during a 2012 event were published, and his password was revealed to be “dadada.” Even when you are the head of a company that handles some of the most private and intimate details of peoples lives, the temptation to chose something easy and memorable wins out over safety.
The only solution is to use a password manager like LastPass, KeePass, 1Password or others. Familiarize yourself with a solution that works with every platform you use (Windows, Mac, Android, iPhone, Linux, etc.), and start the process. It will be time consuming and awkward to begin with, but it will make your life easier in the long run. Ultimately there is nothing as awkward and inconvenient as identity theft.
Additionally, there is another feature available to users today that Aaron Barr did no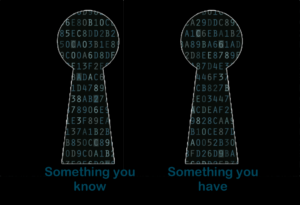 t have in 2011: Two-Factor Authentication. This basically means that when a user logs into a service for the first time in a new place, they are required to have something other than just the password. The “second factor†can be a number of things, from an SMS text message that demonstrates you have access to the phone associated with the account, to software called “Google Authenticatorâ€, which creates a rotating number that changes every minute, to a hardware dongle that you need to login to your account. With a “second factorâ€, it does not matter as much if your password is compromised because the password alone is not enough to gain access to your accounts.
t have in 2011: Two-Factor Authentication. This basically means that when a user logs into a service for the first time in a new place, they are required to have something other than just the password. The “second factor†can be a number of things, from an SMS text message that demonstrates you have access to the phone associated with the account, to software called “Google Authenticatorâ€, which creates a rotating number that changes every minute, to a hardware dongle that you need to login to your account. With a “second factorâ€, it does not matter as much if your password is compromised because the password alone is not enough to gain access to your accounts.
While the MySpace breach was alarming, it should be a wake-up call for all of us to review our security footprint. Of course, long term MySpace users should be encouraged to change their password, not just on this site but everywhere that same password was used.  More importantly, we should look at how we use passwords, and cease the practice of password recycling. While updating your passwords to something more secure, and adopting and relying upon a password manager may be time consuming, it is far easier to change this habit than it would be to recover from identity theft.
This is a common problem, a problem to which even the most technically adept are not immune. With a small investment in time, and little investment in changing behavior, can prevent much more serious consequences and feel the pride that you practicing better online security than Mark Zuckerberg.